设置 Auth0 单点登录
OpenID Connect (OIDC) 是位于 OAuth 2.0 协议 之上的简单身份层。它允许客户端根据身份提供商执行的身份验证来验证最终用户的身份,并以可互操作和类似 REST 的方式获取有关最终用户的基本个人资料信息。通过 APISIX 和 Auth0,你可以实施基于 OIDC 的身份验证流程来保护你的 API 并启用单点登录 (SSO)。
Auth0 是一种高度灵活的身份即服务 (IDaaS) 服务,由 身份行业标准 支持。它提供了一个可以根据你自己的品牌进行定制的图形界面,并提供多种登录选项,例如电子邮件、社交登录、无密码身份验证、生物识别登录、通过 SMS/WhatsApp 发送的一次性密码 (OTP) 和多因素身份验证 (MFA)。
本指南将向你展示如何使用两种身份验证方法将 APISIX 与 Auth0 集成:使用用户凭证进行身份验证 和 使用客户端凭证进行身份验证。
前置条件
配置 Auth0
创建 Auth0 API
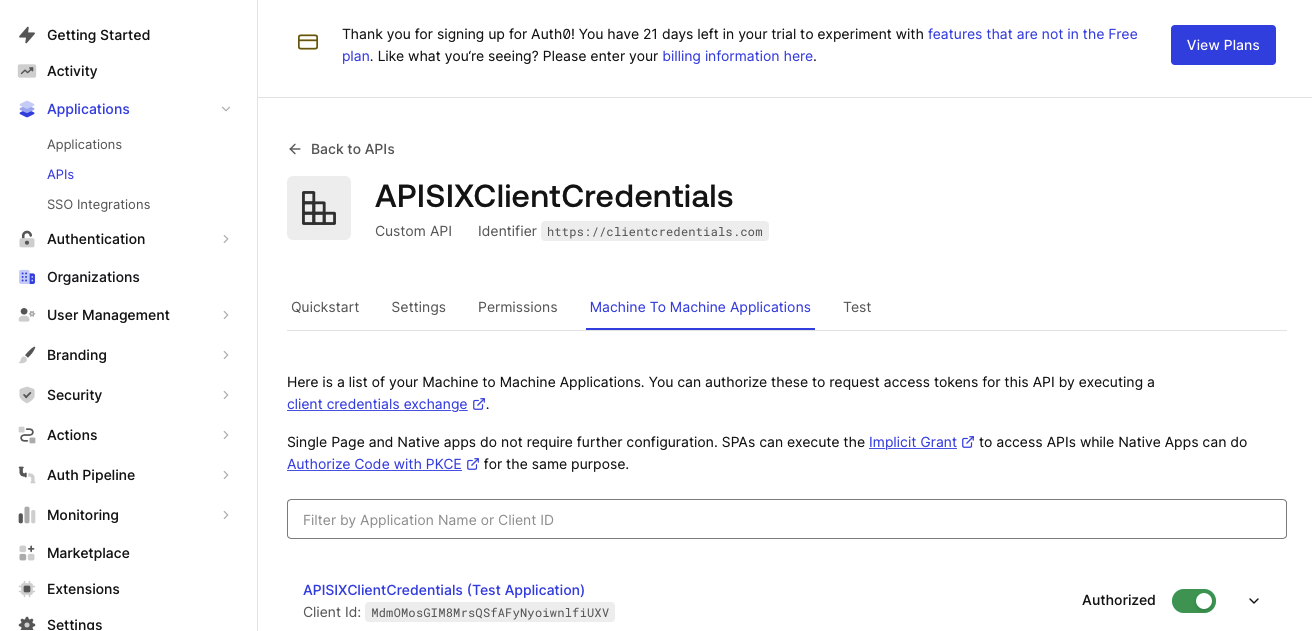
登录到 Auth0 控制台。单击 Applications > APIs > Create API,创建一个名称为 APISIXClientCredentials、标识符为 https://clientcredentials.com 的新 API。单击 Create 保存更改。
配置 Auth0 应用程序
创建 API 后,单击 Machine to Machine Applications 选项卡。你应该会看到一个自动创建的测试应用程序,该应用程序已获授权访问该 API。
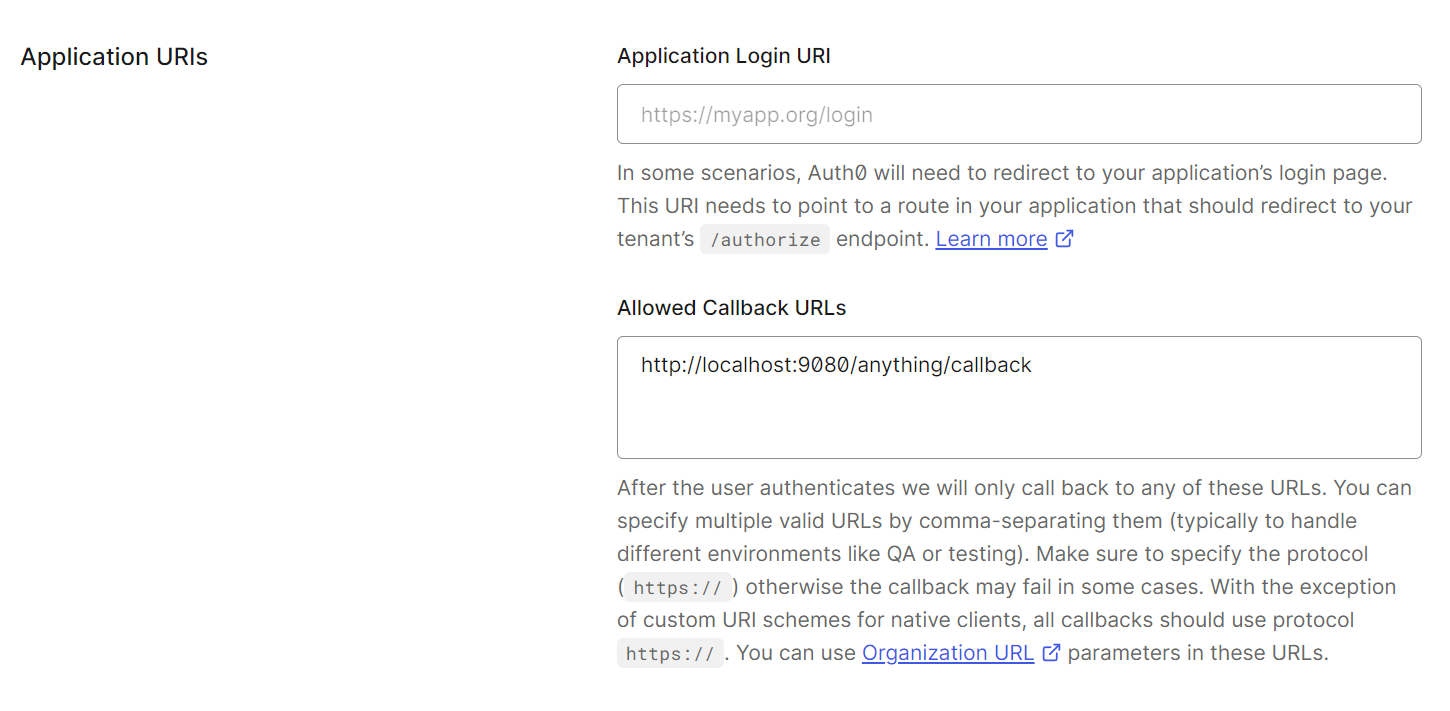
单击 APISIXClientCredentials (Test Application) 以配置应用程序设置。向下滚动到 Application URIs 部分,将回调 URL http://localhost:9080/anything/callback 添加到 Allowed Callback URLs 字段中。这是测试应用程序在使用 Auth0 成功进行身份验证后将用户重定向到的地址。
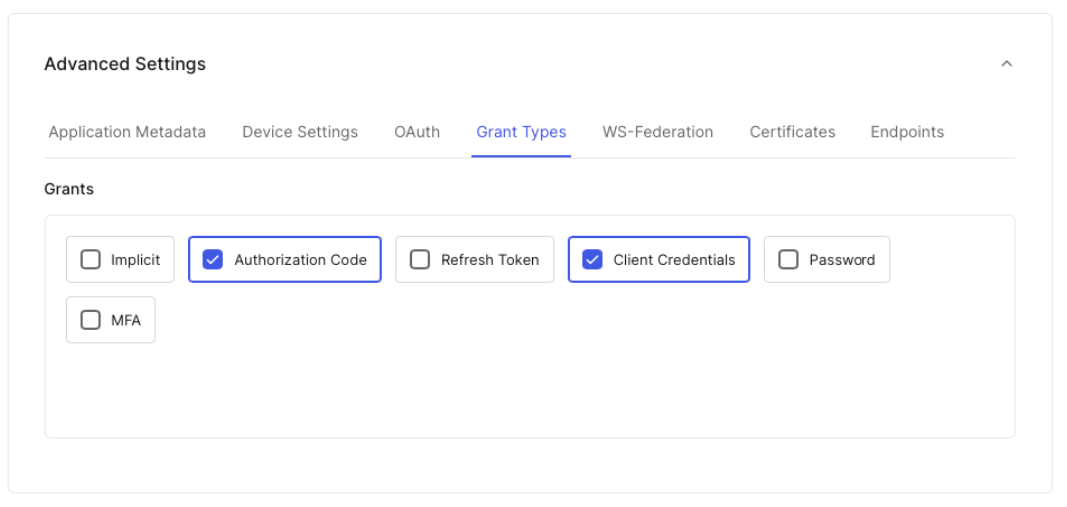
在同一页面的底部,展开 Advanced Settings,选择 Grant Types 选项卡,��然后选中 Authorization Code 选项。单击 Save Changes。
向上滚动到 Basic Information 部分,找到应用程序的 Domain、Client ID 和 Client Secret。将它们保存到环境变量:
# 替换为你的配置值
export AUTH0_DOMAIN=dev-4lg4ifsq4jvpn7s2.us.auth0.com
export AUTH0_CLIENT_ID=eAC8UTVPFirufOh4a1DZtc7F20z7yGuv
export AUTH0_CLIENT_SECRET=52uF_dp5uIOd3TuFyA2Za5tKjB_vEDlwwO08YaHLJw5E93EBmXK8NqlBPCHmOgvc
配置 APISIX
在本节中,你将创建一个带有 OIDC 的路由,该路由将客户端请求转发到 httpbin.org,这是一个公共 HTTP 请求和响应服务。
httpbin.org 的路由 /anything/{anything} 以 JSON 类型返回请求数据中传递的任何内容,例如方法、参数和标头。
启用 OIDC 插件
创建一个路由并启用 openid-connect 插件,如下所示:
- Admin API
- ADC
- Ingress Controller
curl -i "http://127.0.0.1:9180/apisix/admin/routes" -X PUT -d '
{
"id": "auth-with-oidc",
"uri":"/anything/*",
"plugins": {
"openid-connect": {
"client_id": "'"$AUTH0_CLIENT_ID"'",
"client_secret": "'"$AUTH0_CLIENT_SECRET"'",
"discovery": "https://'"$AUTH0_DOMAIN"'/.well-known/openid-configuration",
"scope": "openid profile",
"redirect_uri": "http://localhost:9080/anything/callback",
"bearer_only": false,
"session": {
"secret": "f86cf31663a9c9fa0a28c2cc78badef1"
}
}
},
"upstream":{
"type":"roundrobin",
"nodes":{
"httpbin.org:80":1
}
}
}'
❶ client_id:Auth0 客户端 ID。
❷ client_secret:Auth0 客户端 secret。
❸ discovery:Auth0 的 OIDC 发现文档 URI。
❹ redirect_uri:使用 Auth0 身份验证后重定向到的 URI。
❺ bearer_only:对于授权码流,设置为 false。
❻ session.secret:替换为你用于会话加密和 HMAC 操作的密钥。当 bearer_only 为 false 时为必需。
services:
- name: httpbin Service
routes:
- uris:
- /anything/*
name: auth-with-oidc
plugins:
openid-connect:
client_id: 'eAC8UTVPFirufOh4a1DZtc7F20z7yGuv'
client_secret: '52uF_dp5uIOd3TuFyA2Za5tKjB_vEDlwwO08YaHLJw5E93EBmXK8NqlBPCHmOgvc'
discovery: 'https://dev-4lg4ifsq4jvpn7s2.us.auth0.com/.well-known/openid-configuration'
scope: openid profile
redirect_uri: 'http://localhost:9080/anything/callback'
bearer_only: false
session:
secret: 'f86cf31663a9c9fa0a28c2cc78badef1'
upstream:
type: roundrobin
nodes:
- host: httpbin.org
port: 80
weight: 1
❶ client_id:Auth0 客户端 ID。
❷ client_secret:Auth0 客户端 secret。
❸ discovery:Auth0 的 OIDC 发现文档 URI。
❹ redirect_uri:使用 Auth0 身份验证后重定向到的 URI。
❺ bearer_only:对于授权码流,设置为 false。
❻ session.secret:替换为你用于会话加密和 HMAC 操作的密钥。当 bearer_only 为 false 时为必需。
Synchronize the configuration to APISIX:
adc sync -f adc.yaml
- Gateway API
- APISIX CRD
apiVersion: apisix.apache.org/v1alpha1
kind: PluginConfig
metadata:
namespace: ingress-apisix
name: auth-plugin-config
spec:
plugins:
- name: openid-connect
config:
client_id: eAC8UTVPFirufOh4a1DZtc7F20z7yGuv
client_secret: 52uF_dp5uIOd3TuFyA2Za5tKjB_vEDlwwO08YaHLJw5E93EBmXK8NqlBPCHmOgvc
discovery: https://dev-4lg4ifsq4jvpn7s2.us.auth0.com/.well-known/openid-configuration
scope: openid profile
redirect_uri: http://localhost:9080/anything/callback
bearer_only: false
session:
secret: f86cf31663a9c9fa0a28c2cc78badef1
---
apiVersion: v1
kind: Service
metadata:
namespace: ingress-apisix
name: httpbin-external-domain
spec:
type: ExternalName
externalName: httpbin.org
---
apiVersion: gateway.networking.k8s.io/v1
kind: HTTPRoute
metadata:
namespace: ingress-apisix
name: auth-with-oidc
spec:
parentRefs:
- name: apisix
rules:
- matches:
- path:
type: PathPrefix
value: /anything/*
filters:
- type: ExtensionRef
extensionRef:
group: apisix.apache.org
kind: PluginConfig
name: auth-plugin-config
backendRefs:
- name: httpbin-external-domain
port: 80
apiVersion: apisix.apache.org/v2
kind: ApisixUpstream
metadata:
namespace: ingress-apisix
name: httpbin-external-domain
spec:
externalNodes:
- type: Domain
name: httpbin.org
---
apiVersion: apisix.apache.org/v2
kind: ApisixRoute
metadata:
namespace: ingress-apisix
name: auth-with-oidc
spec:
ingressClassName: apisix
http:
- name: auth-with-oidc
match:
paths:
- /anything/*
plugins:
- name: openid-connect
enable: true
config:
client_id: eAC8UTVPFirufOh4a1DZtc7F20z7yGuv
client_secret: 52uF_dp5uIOd3TuFyA2Za5tKjB_vEDlwwO08YaHLJw5E93EBmXK8NqlBPCHmOgvc
discovery: https://dev-4lg4ifsq4jvpn7s2.us.auth0.com/.well-known/openid-configuration
scope: openid profile
redirect_uri: http://localhost:9080/anything/callback
bearer_only: false
session:
secret: f86cf31663a9c9fa0a28c2cc78badef1
upstreams:
- name: httpbin-external-domain
❶ client_id:Auth0 客户端 ID。
❷ client_secret:Auth0 客户端 secret。
❸ discovery:Auth0 的 OIDC 发现文档 URI。
❹ redirect_uri:使用 Auth0 身份验证后重定向到的 URI。
❺ bearer_only:对于授权码流,设置为 false。
❻ session.secret:替换为你用于�会话加密和 HMAC 操作的密钥。当 bearer_only 为 false 时为必需。
Apply the configuration to your cluster:
kubectl apply -f oidc-route.yaml
使用用户凭证进行身份验证
在浏览器中导航到 http://localhost:9080/anything/test。你应该被重定向到 Auth0 通用登录 页面:
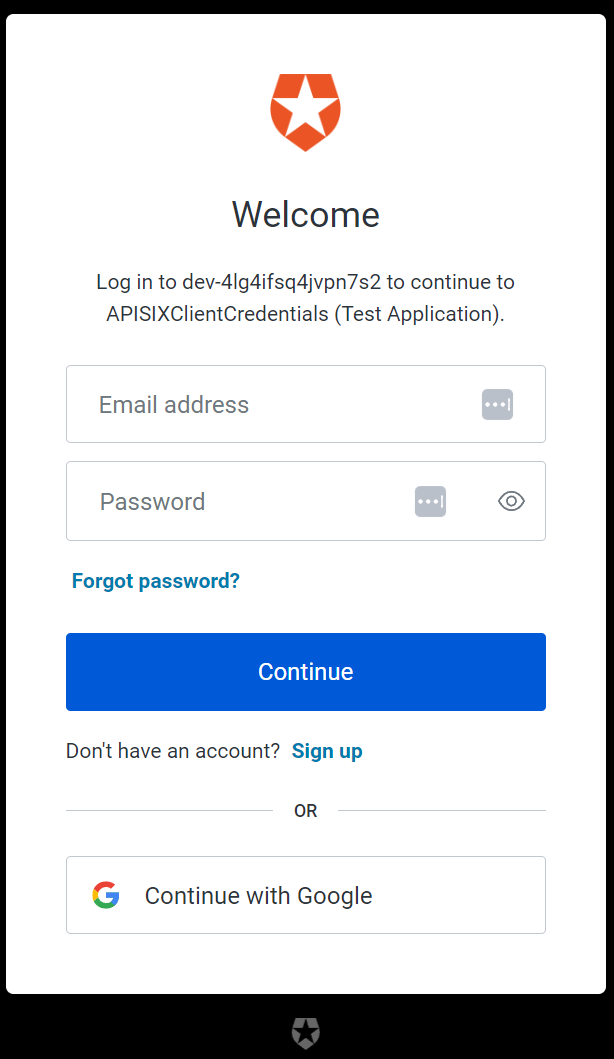
使用你的凭证登录。如果成功,请求将被转发到 httpbin.org,你应该看到类似以下的响应:
{
"args": {},
"data": "",
"files": {},
"form": {},
"headers": {
"Accept": "text/html..."
...
},
"json": null,
"method": "GET",
"origin": "127.0.0.1, 59.71.xxx.xxx",
"url": "http://127.0.0.1/anything/test"
}
使用客户端凭证进行身份验证
客户端凭证流 涉及机器对机器 (M2M) 应用程序在没有用户参与的情况下与服务交换凭证。
在本节中,你将使用额外的 OIDC 配置更新现有路由,并使用访问令牌向 Auth0 进行身份验证。
更新 OIDC 插件
更新路由上的 OIDC 插件以使用身份服务器的 JWKS 端点来验证令牌:
- Admin API
- ADC
- Ingress Controller
curl -i "http://127.0.0.1:9180/apisix/admin/routes/auth-with-oidc" -X PATCH -d '
{
"plugins": {
"openid-connect": {
"use_jwks": true
}
}
}'
❶ use_jwks:允许使用身份提供商的 JWKS 端点来验证令牌。
services:
- name: httpbin Service
routes:
- uris:
- /anything/*
name: auth-with-oidc
plugins:
openid-connect:
use_jwks: true
client_id: 'eAC8UTVPFirufOh4a1DZtc7F20z7yGuv'
client_secret: '52uF_dp5uIOd3TuFyA2Za5tKjB_vEDlwwO08YaHLJw5E93EBmXK8NqlBPCHmOgvc'
discovery: 'https://dev-4lg4ifsq4jvpn7s2.us.auth0.com/.well-known/openid-configuration'
scope: openid profile
redirect_uri: 'http://localhost:9080/anything/callback'
bearer_only: false
session:
secret: 'f86cf31663a9c9fa0a28c2cc78badef1'
upstream:
type: roundrobin
nodes:
- host: httpbin.org
port: 80
weight: 1
❶ use_jwks:允许使用身份提供商的 JWKS 端点来验证令牌。
Synchronize the configuration to APISIX:
adc sync -f adc.yaml
- Gateway API
- APISIX CRD
apiVersion: apisix.apache.org/v1alpha1
kind: PluginConfig
metadata:
namespace: ingress-apisix
name: auth-plugin-config
spec:
plugins:
- name: openid-connect
config:
use_jwks: true
client_id: eAC8UTVPFirufOh4a1DZtc7F20z7yGuv
client_secret: 52uF_dp5uIOd3TuFyA2Za5tKjB_vEDlwwO08YaHLJw5E93EBmXK8NqlBPCHmOgvc
discovery: https://dev-4lg4ifsq4jvpn7s2.us.auth0.com/.well-known/openid-configuration
scope: openid profile
redirect_uri: http://localhost:9080/anything/callback
bearer_only: false
session:
secret: f86cf31663a9c9fa0a28c2cc78badef1
---
apiVersion: v1
kind: Service
metadata:
namespace: ingress-apisix
name: httpbin-external-domain
spec:
type: ExternalName
externalName: httpbin.org
---
apiVersion: gateway.networking.k8s.io/v1
kind: HTTPRoute
metadata:
namespace: ingress-apisix
name: auth-with-oidc
spec:
parentRefs:
- name: apisix
rules:
- matches:
- path:
type: PathPrefix
value: /anything/*
filters:
- type: ExtensionRef
extensionRef:
group: apisix.apache.org
kind: PluginConfig
name: auth-plugin-config
backendRefs:
- name: httpbin-external-domain
port: 80
apiVersion: apisix.apache.org/v2
kind: ApisixUpstream
metadata:
namespace: ingress-apisix
name: httpbin-external-domain
spec:
externalNodes:
- type: Domain
name: httpbin.org
---
apiVersion: apisix.apache.org/v2
kind: ApisixRoute
metadata:
namespace: ingress-apisix
name: auth-with-oidc
spec:
ingressClassName: apisix
http:
- name: auth-with-oidc
match:
paths:
- /anything/*
plugins:
- name: openid-connect
enable: true
config:
use_jwks: true
client_id: eAC8UTVPFirufOh4a1DZtc7F20z7yGuv
client_secret: 52uF_dp5uIOd3TuFyA2Za5tKjB_vEDlwwO08YaHLJw5E93EBmXK8NqlBPCHmOgvc
discovery: https://dev-4lg4ifsq4jvpn7s2.us.auth0.com/.well-known/openid-configuration
scope: openid profile
redirect_uri: http://localhost:9080/anything/callback
bearer_only: false
session:
secret: f86cf31663a9c9fa0a28c2cc78badef1
upstreams:
- name: httpbin-external-domain
❶ use_jwks:允许使用身份提供商的 JWKS 端点来验证令牌。
Apply the configuration to your cluster:
kubectl apply -f oidc-route.yaml
测试访问令牌
获取 APISIXClientCredentials 测试应用程序的访问令牌:
curl -i "https://$AUTH0_DOMAIN/oauth/token" -X POST \
-H 'content-type: application/json' \
-d '{
"client_id":"'$AUTH0_CLIENT_ID'",
"client_secret":"'$AUTH0_CLIENT_SECRET'",
"audience":"https://clientcredentials.com",
"grant_type":"client_credentials"
}'
你应该看到类似以下的响应:
{
"access_token":"eyJhbGciOiJSUzI1NiIsInR5cCI6IkpXVCIsImtpZCI6Ikc2elVuYzgtM0JrVlgtZmdnMTdKNSJ9.eyJpc3MiOiJodHRwczovL2Rldi00bGc0aWZzcTRqdnBuN3MyLnVzLmF1dGgwLmNvbS8iLCJzdWIiOiJlQUM4VVRWUEZpcnVmT2g0YTFEWnRjN0YyMHo3eUd1dkBjbGllbnRzIiwiYXVkIjoiaHR0cHM6Ly9jbGllbnRjcmVkZW50aWFscy5jb20iLCJpYXQiOjE2OTMwNDAwMjcsImV4cCI6MTY5MzEyNjQyNywiYXpwIjoiZUFDOFVUVlBGaXJ1Zk9oNGExRFp0YzdGMjB6N3lHdXYiLCJndHkiOiJjbGllbnQtY3JlZGVudGlhbHMifQ.aePOiFlW0q0mlrQwKdtP1MGfY2nX7TSnTrEjoJI03aG7lBCHhPX_WwszhYvtM5c_cyQtcI6R4ibPskpTssdEXGCe2wbOhstPWeIb9rCFf_kA_g0p1wDM8j8egRfl7PLmFffaEmU0eNrgmjTgYQ0Erk63XDykPFOFWiQKPfDQ2hf4jz_3J_VKNqwy7yQuxisnD5TysybGmrONoiBjYLGIymk1ii-qKEoNt5_DRv10aSBwyRtxDZbiwhAKcWNO7zLaJVmZZLg1aTiRYxgIOU-_AP4iAR6Y4vK_GxyHqf7G6j6yH8wqCj8Nm2bLEg8Gqb9Fd-xbpbQCiC3X14ja5NTYtw",
"expires_in":86400,
"token_type":"Bearer"
}
将访问令牌保存到环境变量:
# 替换为你的访问令牌
export ACCESS_TOKEN="eyJhbGciOiJSUzI1NiIsInR5cCI6IkpXVCIsImtpZCI6Ikc2elVuYzgtM0JrVlgtZmdnMTdKNSJ9.eyJpc3MiOiJodHRwczovL2Rldi00bGc0aWZzcTRqdnBuN3MyLnVzLmF1dGgwLmNvbS8iLCJzdWIiOiJlQUM4VVRWUEZpcnVmT2g0YTFEWnRjN0YyMHo3eUd1dkBjbGllbnRzIiwiYXVkIjoiaHR0cHM6Ly9jbGllbnRjcmVkZW50aWFscy5jb20iLCJpYXQiOjE2OTMwNDAwMjcsImV4cCI6MTY5MzEyNjQyNywiYXpwIjoiZUFDOFVUVlBGaXJ1Zk9oNGExRFp0YzdGMjB6N3lHdXYiLCJndHkiOiJjbGllbnQtY3JlZGVudGlhbHMifQ.aePOiFlW0q0mlrQwKdtP1MGfY2nX7TSnTrEjoJI03aG7lBCHhPX_WwszhYvtM5c_cyQtcI6R4ibPskpTssdEXGCe2wbOhstPWeIb9rCFf_kA_g0p1wDM8j8egRfl7PLmFffaEmU0eNrgmjTgYQ0Erk63XDykPFOFWiQKPfDQ2hf4jz_3J_VKNqwy7yQuxisnD5TysybGmrONoiBjYLGIymk1ii-qKEoNt5_DRv10aSBwyRtxDZbiwhAKcWNO7zLaJVmZZLg1aTiRYxgIOU-_AP4iAR6Y4vK_GxyHqf7G6j6yH8wqCj8Nm2bLEg8Gqb9Fd-xbpbQCiC3X14ja5NTYtw"
使用有效访问令牌向路由发送请求:
curl -i "http://127.0.0.1:9080/anything/test" -H "Authorization: Bearer $ACCESS_TOKEN"
HTTP/1.1 200 OK 响应验证了 API 调用已获授权。
下一步
APISIX 支持与许多其他 OIDC 身份提供商集成,例如 Keycloak、Authgear、Microsoft Entra ID (Azure AD) 和 Google。