与 Coraza 集成
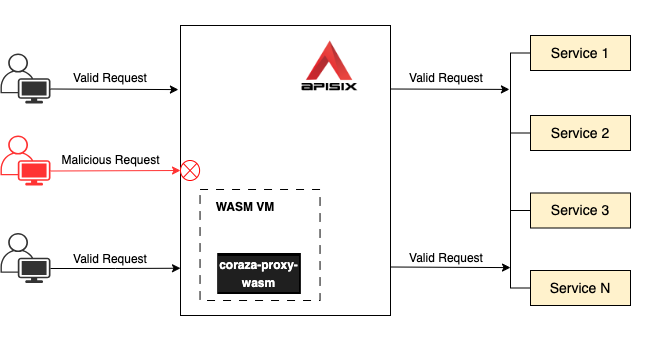
随着技术的快速发展,保护 API 变得越来越重要。APISIX 支持通过使用 coraza-proxy-wasm 与 Coraza 集成,以提供可靠的安全保护并确保 API 服务的完整性和可靠性。
Coraza 是一个开源、企业级、高性能的 Web 应用程序防火墙 (WAF)。它旨在通过过滤和监控 Web 应用程序与互联网之间的 HTTP/HTTPS 通信,保护 Web 应用程序免受各种网络攻击。通过与 Coraza 集成,APISIX 显著增强了保护上游服务的能力。
本指南将向你展示如何启用 coraza-proxy-wasm 以将 APISIX 与 Coraza WAF 集成来保护上游服务。
前置条件
- 安装 Docker。
- 安装 cURL 以向服务发送请求进行验证。
- 安装 ZIP 以解压缩 发布页面 中的
coraza-proxy-wasm二进制文件。 - 按照 快速入门教程 在 Docker 中启动一个新的 APISIX 实例。
下载 coraza-proxy-wasm
从 发布页面 下载 coraza-proxy-wasm 并解压缩:
wget https://github.com/corazawaf/coraza-proxy-wasm/releases/download/0.4.0/coraza-proxy-wasm-0.4.0.zip
unzip coraza-proxy-wasm-0.4.0.zip
将 coraza-proxy-wasm.wasm 复制到 /usr/local/bin 目录:
docker cp /path/to/coraza-proxy-wasm.wasm apisix-quickstart:/usr/local/bin/
在 APISIX 中加载 coraza-proxy-wasm
通过添加 coraza-proxy-wasm 配置更新 config.yaml 配置文件:
docker exec apisix-quickstart /bin/bash -c "echo '
wasm:
plugins:
- name: coraza-filter
priority: 7999
file: /usr/local/bin/coraza-proxy-wasm.wasm
' >> /usr/local/apisix/conf/config.yaml"
❶ name:对应于 coraza-proxy-wasm 的 APISIX 插件名称。
❷ priority:插件的 执行优先级。
❸ file:coraza-proxy-wasm 的绝对路径。
重新加载 APISIX 以使配置更改生效:
docker exec apisix-quickstart apisix reload
配置特定安全规则
创建一个路由并启用 coraza-filter:
- Admin API
- ADC
curl -i "http://127.0.0.1:9180/apisix/admin/routes/" -X PUT -d '
{
"id": "getting-started-waf",
"uri": "/anything/*",
"plugins": {
"coraza-filter": {
"conf": {
"directives_map": {
"default": [
"SecDebugLogLevel 9",
"SecRuleEngine On",
"SecRule REQUEST_URI \"@beginsWith /anything/archive\" \"id:101,phase:1,t:lowercase,deny\""
]
},
"default_directives": "default"
}
}
},
"upstream": {
"type": "roundrobin",
"nodes": {
"httpbin.org:80": 1
}
}
}'
❶ SecDebugLogLevel:配置调试日志级别。有关详细信息,请参阅 SecDebugLogLevel。
❷ SecRuleEngine:配置规则引擎。有关详细信息,请参阅 SecRuleEngine。
❸ SecRule:检查 HTTP 请求的 URI 值,看 URI 值是否以 /anything/archive 开头。如果匹配,请求将被拒绝。有关详细信息,请参阅 SecRule。
services:
- name: httpbin Service
routes:
- uris:
- /anything/*
name: getting-started-waf
plugins:
coraza-filter:
conf:
directives_map:
default:
- SecDebugLogLevel 9
- SecRuleEngine On
- SecRule REQUEST_URI "@beginsWith /anything/archive" "id:101,phase:1,t:lowercase,deny"
default_directives: default
upstream:
type: roundrobin
nodes:
- host: httpbin.org
port: 80
weight: 1
❶ SecDebugLogLevel:配置调试日志级别。有关详细信息,请参阅 SecDebugLogLevel。
❷ SecRuleEngine:配置规则引擎。有关详细信息,请参阅 SecRuleEngine。
❸ SecRule:检查 HTTP 请求的 URI 值,看 URI 值是否以 /anything/archive 开头。如果匹配,请求将被拒绝。有关详细信息,请参阅 SecRule。
将配置同步到 APISIX:
adc sync -f adc.yaml
验证
向路由发送请求以验证 URI 以 anything/archive 开头的 HTTP 请求是否会被拒绝:
curl -i "http://localhost:9080/anything/archive/test"
你应该收到 HTTP/1.1 403 Forbidden 响应。
向路由发送请求以验证 URI 以 anything 开头的 HTTP 请求是否会被允许:
curl -i "http://localhost:9080/anything/public"
你应该收到 HTTP/1.1 200 OK 响应。
配置 OWASP 核心规则集
你还可以按如下方式在路由上配置整个 OWASP 核心规则集 (CRS):
- Admin API
- ADC
curl -i "http://127.0.0.1:9180/apisix/admin/routes/" -X PUT -d '
{
"id": "getting-started-waf",
"uri": "/anything/*",
"plugins": {
"coraza-filter": {
"conf": {
"directives_map": {
"default": [
"SecDebugLogLevel 9",
"SecRuleEngine On",
"Include @crs-setup-conf",
"Include @owasp_crs/*.conf"
]
},
"default_directives": "default"
}
}
},
"upstream": {
"type": "roundrobin",
"nodes": {
"httpbin.org:80": 1
}
}
}'
❶ 包含 @crs-setup-conf 以支持 CRS。
❷ 包含所有 CRS 规则。你也可以包含特定规则,例如 @owasp_crs/REQUEST-941-APPLICATION-ATTACK-XSS.conf。查看 所有可用规则。
services:
- name: httpbin Service
routes:
- uris:
- /anything/*
name: getting-started-waf
plugins:
coraza-filter:
conf:
directives_map:
default:
- SecDebugLogLevel 9
- SecRuleEngine On
- Include @crs-setup-conf
- Include @owasp_crs/*.conf
default_directives: default
upstream:
type: roundrobin
nodes:
- host: httpbin.org
port: 80
weight: 1
❶ 包含 @crs-setup-conf 以支持 CRS。
❷ 包含所有 CRS 规则。你也可以包含特定规则,例如 @owasp_crs/REQUEST-941-APPLICATION-ATTACK-XSS.conf。查看 所有可用规则。
将配置同步到 APISIX:
adc sync -f adc.yaml
验证
向路由发送带有潜在 XSS 攻击的请求:
curl -i "http://localhost:9080/anything/public" -H "Cookie: <body onload='alert(xss)'>"
你应该收到 HTTP/1.1 403 Forbidden 响应并在日志中观察到以下内容:
2023/12/21 02:27:14 [emerg] 130#130: *116868 [client ""] Coraza: Warning. NoScript XSS InjectionChecker: HTML Injection [file "@owasp_crs/REQUEST-941-APPLICATION-ATTACK-XSS.conf"] [line "7529"] [id "941160"] [rev ""] [msg "NoScript XSS InjectionChecker: HTML Injection"] [data "Matched Data: <body found within REQUEST_COOKIES_NAMES:<body onload: <body onload"] [severity "critical"] [ver "OWASP_CRS/4.0.0-rc2"] [maturity "0"] [accuracy "0"] [tag "application-multi"] [tag "language-multi"] [tag "platform-multi"] [tag "attack-xss"] [tag "paranoia-level/1"] [tag "OWASP_CRS"] [tag "capec/1000/152/242"] [hostname ""] [uri "/anything/public"] [unique_id "vXZLznnuwaZHkjIBXyN"], client: 172.24.0.1, server: _, request: "GET /anything/public HTTP/1.1", host: "localhost:9080"
2023/12/21 02:27:14 [emerg] 130#130: *116868 [client ""] Coraza: Warning. Javascript method detected [file "@owasp_crs/REQUEST-941-APPLICATION-ATTACK-XSS.conf"] [line "8023"] [id "941390"] [rev ""] [msg "Javascript method detected"] [data "Matched Data: alert( found within REQUEST_COOKIES:<body onload: 'alert(xss)'>"] [severity "critical"] [ver "OWASP_CRS/4.0.0-rc2"] [maturity "0"] [accuracy "0"] [tag "application-multi"] [tag "language-multi"] [tag "attack-xss"] [tag "paranoia-level/1"] [tag "OWASP_CRS"] [tag "capec/1000/152/242"] [hostname ""] [uri "/anything/public"] [unique_id "vXZLznnuwaZHkjIBXyN"], client: 172.24.0.1, server: _, request: "GET /anything/public HTTP/1.1", host: "localhost:9080"
2023/12/21 02:27:14 [emerg] 130#130: *116868 [client ""] Coraza: Access denied (phase 1). Inbound Anomaly Score Exceeded in phase 1 (Total Score: 10) [file "@owasp_crs/REQUEST-949-BLOCKING-EVALUATION.conf"] [line "11098"] [id "949111"] [rev ""] [msg "Inbound Anomaly Score Exceeded in phase 1 (Total Score: 10)"] [data ""] [severity "emergency"] [ver "OWASP_CRS/4.0.0-rc2"] [maturity "0"] [accuracy "0"] [tag "anomaly-evaluation"] [hostname ""] [uri "/anything/public"] [unique_id "vXZLznnuwaZHkjIBXyN"], client: 172.24.0.1, server: _, request: "GET /anything/public HTTP/1.1", host: "localhost:9080"
这验证了 CRS 规则已生效以保护你的路由。
下一步
APISIX 还支持与长亭 WAF 和流行的云供应商提供的其他 WAF 集成。请参阅本章中的其他指南以了解更多信息(即将推出)。